July 13, 2018
If you have ever used Docker or any other Linux OCI container system, you inevitably have incurred in the following error:
x509: failed to load system roots and no roots provided
This message is remembering you that you forgot to provide Root Certificate Authorities to your application.
There are two different ways to solve this:
- mount the /etc/ssl/certs folder from the machine where the container is running
- bundling the root CAs in your image
As you may imagine from the title, I believe that the second option is by far better than the first one.
Read More 
June 27, 2018
Lately, all website are urging their users to enable second-factors.
The push for multi-factor logins is a good thing from my point of view, since the people are putting more and more details of their life online and is a good thing that companies start to understand the security implication of this and are trying to teach their users good security practices.
The real problem is what is defined as second-factor.
The possible factors are three:
Read More 
December 21, 2017
A few months ago, I posted how to create a PKI in Go.
Today I’d like to add share a useful function (at least from my point of view) that I found myself to write.
The problem arose when I had a function that required as input a *pem.Block of the public key, but all I had was the PEM file containing, as you can imagine:
- the Private Key
- the Public Key
- the CA Public Key
I think this is a typical situation, and for this, I’d like to share a function I wrote to extract it.
I know that it’s probably not perfect, but it could be a good starting point for many of you, and if you have suggestions, please leave a comment down below or send me an email, and I’ll update the post!
Read More 
November 3, 2017
Authentication factors
One of the common way to create more secure authentication in systems is adding more “factors”, creating in this way a Multi-Factor Authentication (MFA).
The idea behind MFA is that there are many different ways to authenticate a user, and those can be split in different “categories” based on the kind of challenge we require.
Generally speaking, it’s common to divide the authentication methods in mainly three categories:
Read More 
June 5, 2017
Lately I have been programming quite a bit and - for the first time - I have used Golang doing so.
Go is a very nice language and really helped me with the development.
One of the reasons why I have enjoyed this much Go is the standard library, which is amazing.
I would like to share today the easiness of creating a basic Certificate Authority and signed certificates in Go.
Read More 
April 13, 2016
Yesterday, Let’s Encrypt moved from beta to GA.
During the beta phase, which started last September, more than 1.7 million certificates were issued.
I think this is a crucial step for the project and overall for the Internet as well.
Until now, the only way to obtain a valid TLS certificate was to pay a CA.
This artificial constraint made no sense since the CAs were forcing users to buy an insurance policy that made no sense (and often, it was completely worthless).
Read More 
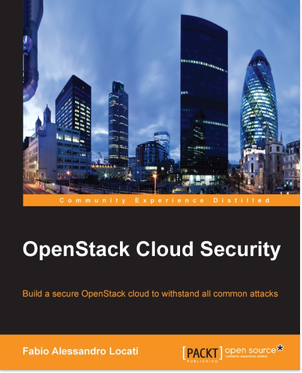
Published on July 28, 2015
Authored by Fabio Alessandro Locati
Published by Packt Publishing Limited
OpenStack is a system that controls large pools of computing and networking resources, along with cloud storage, allowing its users to provision resources through a user-friendly interface.
OpenStack helps developers with features such as rolling upgrades, federated identity, and software reliability.
You will begin with basic security policies, such as MAC, MLS, and MCS, and explore the structure of OpenStack and virtual networks with Neutron.
Next, you will configure secure communications on the OpenStack API with HTTP connections.
You will also learn how to set OpenStack Keystone and OpenStack Horizon and gain a deeper understanding of the similarities/differences between OpenStack Cinder and OpenStack Swift.
Read More
Buy it on Packt
Buy it on Amazon 
May 20, 2015
Today it was published a new kind of downgrade attack against TLS: logjam.
The attack relies on the fact that for Diffie-Hellman key exchanges, a prime is necessary.
Many applications use a pre-generated prime to speed up the Diffie-Hellman process.
Using a pre-generated prime is not a security issue by itself, but it can become one if coupled with a server that accepts very short Diffie-Hellman keys such as the 512 bits ones (the maximum allowed for DHE_EXPORT).
Read More 
April 2, 2014
I usually don’t start with this, but lately I had some time constraints that made me wondering if is right to use so much time reading books. The Wireshark Field Guide Analyzing and Troubleshooting Network Traffic by Robert J. Shimonski is only 149 pages long (if we cut the introduction, indexes, etc. it boils down to 128 pages). This is a really short book and I have really appreciated this fact. Wireshark is a very useful and powerful tool, but many people do not need to know everything about it. If you need to know everything about wireshark, the best option is to download the source and read it, but this is not the case for 99.99% of the people interested in Wireshark.
Read More 
October 16, 2013
A month after the CompTIA Linux+, I decided to do the CompTIA Security+.
As for the Linux+, the Security+ uses on a multiple-choice test.
In this case, I think this kind of exam is a perfect fit since it’s essential that the candidate has and can demonstrate a solid understanding of the theory behind security.
Overall I liked the exam, and I would suggest it to anyone interested in starting a journey in security or wants (or needs) to have a certification that certifies a base knowledge around security.
Read More